In the digital age, IP addresses, network configurations, and security protocols form the backbone of online connectivity. Occasionally, you may encounter seemingly obscure references like 185.63.253.2pp. At first glance, this string may resemble an IP address, but the inclusion of “pp” adds a layer of complexity that demands a closer look.
Whether you’re in IT support, cybersecurity, or simply a tech-savvy user exploring network logs, understanding 185.63.253.2pp is important. In this guide, we break down its possible implications, applications, and how it fits within the modern web environment.
What is 185.63.253.2pp?
The sequence 185.63.253.2pp looks similar to a standard IPv4 address, but the suffix “pp” suggests it’s not a traditional address. Instead, it could be a custom identifier, internal reference, or code used in proxy configurations or private server environments. Some systems may use such formats to distinguish between different data routes or assign roles to certain nodes.
In practical terms, 185.63.253.2pp may represent a network label, a load balancer reference, or even a placeholder in certain applications. It could also be tied to domain mapping, cloud infrastructure, or private port proxies. The “pp” might stand for “proxy point,” “private port,” or another internal designation.
Also, explore Shannon Reardon Swanick: A Detailed Look into the Life and Career
Where Is 185.63.253.2pp Typically Used?
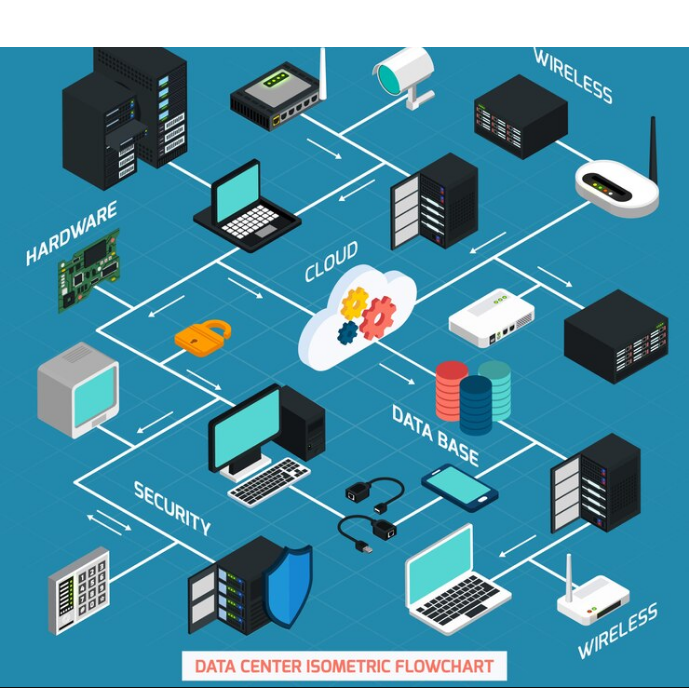
The use of 185.63.253.2pp is more common in corporate networks, data centers, or cloud-based service frameworks. Here’s where it might appear:
-
Server Configuration Files: IT professionals may use labels like 185.63.253.2pp in backend configurations for routing or logging purposes.
-
Proxy Networks: This format is potentially used in proxy servers to differentiate between virtual interfaces or port-forwarding systems.
-
Cybersecurity Platforms: Analysts might flag IP-like strings such as 185.63.253.2pp when monitoring anomalous activity, especially in logs or packet captures.
-
Software Testing Environments: Developers sometimes use these identifiers for testing environments, sandbox setups, or virtual networks.
The Role of IP-like Identifiers in Network Management
Modern network infrastructure relies heavily on clear IP mapping, host naming conventions, and internal identifiers. Labels like 185.63.253.2pp can improve organization, clarity, and efficiency in complex environments.
Here’s how:
-
They enable multi-server coordination.
-
They assist with access control and traffic segmentation.
-
They simplify debugging and log analysis.
-
They reduce human error by providing distinct references.
While not a valid public IP address, 185.63.253.2pp can be an essential part of internal architecture or custom routing logic.
Is 185.63.253.2pp a Security Risk?
As with any non-standard network identifier, it’s important to understand its origin. If 185.63.253.2pp appears unexpectedly in logs or configurations, it could either be a legitimate internal reference or something more concerning like a malicious obfuscation.
When conducting cybersecurity audits, experts often scrutinize unusual entries. If 185.63.253.2pp is not recognized by your systems or documentation, it’s recommended to:
-
Perform a log trace to see where it’s used.
-
Review network activity related to the identifier.
-
Validate it against your known infrastructure map.
Benefits of Custom Network Identifiers Like 185.63.253.2pp
Using custom identifiers, even ones resembling IP addresses, offers several benefits:
-
Enhanced Tracking: Makes it easier to follow network behavior across systems.
-
Customization: Offers flexibility in internal environments and test frameworks.
-
Isolation: Helps isolate network components for security or load testing.
-
Improved Workflow: Streamlines communication between network administrators and developers.
Conclusion
The identifier 185.63.253.2pp exemplifies how network administration often relies on customized notations and references to manage complex systems efficiently. While it may not be a standard IP address, its structure and usage suggest it’s meaningful in internal networks, proxy systems, or security monitoring environments.
Understanding and properly managing identifiers like 185.63.253.2pp ensures that your infrastructure remains organized, secure, and easy to maintain. As with any unusual element in your digital ecosystem, proper documentation and analysis are key to making the most of your network resources.
FAQs
1. Is 185.63.253.2pp a valid public IP address?
No, 185.63.253.2pp is not a standard IP format due to the “pp” suffix. It is likely a custom label or internal identifier.
2. What does the “pp” in 185.63.253.2pp stand for?
The “pp” could represent “proxy point,” “private port,” or another internal designation used in custom configurations.
3. Should I be concerned if I see 185.63.253.2pp in my network logs?
If you’re unfamiliar with it, investigate its source. It could be a legitimate part of your internal infrastructure or an anomaly worth reviewing.
4. Can 185.63.253.2pp be used in a firewall or router setup?
Generally, custom identifiers like 185.63.253.2pp are not recognized by standard networking equipment but may be used in scripts or internal documentation.
5. How do I trace 185.63.253.2pp in my system?
Use network tools to search logs, monitor active connections, or scan configuration files for its presence and role.